Phishing Site Found On Sony Servers
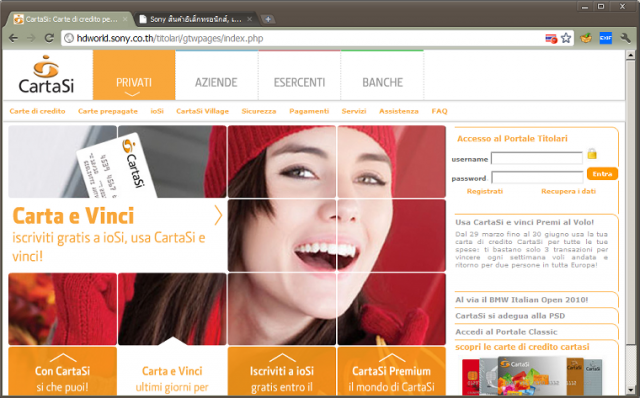
Sony is down for the count yet again. This time it has nothing to do with the PlayStation Network, but a pushing site targeted towards a credit card company.
Pushing attack sites work by tricking people into giving out login credentials and other personal information into a face website that resembles the real site. A simple way to make sure you are on the correct site, check the URL of the page you are on before handing out sensitive information to a website.
Sony’s servers were being used to host a malicious site, which means that when a user navigates to the site the browser thinks the site is valid. But, browsers are catching on quickly to these scams and building in pushing warning systems to prevent these types of attacks. Since these attacks can get by some systems all users should check the URL to make sure they are on the right site.
Sony has been the target of massive attacks. The start of this mess begins back in April, Anonymous began with a DDoS attack against the Sony PlayStation website. After that attack, PlayStation Network was hacked and personal information was stolen, a total of 24.5 million accounts were compromised with the PSN and SOE attacks. We’re not done yet, earlier this week, Sony announced that the PlayStation Network logins were exploited by a flaw in the password recovery system.
The site pictured at the top of this article is targeted towards a credit card company outside of the United States. It is a direct copy of the actual site and tricks users to try to login.
Remember, be warned to what sites you are giving your personal information out to.




